Google Just Moved Q-Day — Every ECC Chain Now Has a Deadline
On March 31, 2026, Ryan Babbush and Hartmut Neven of Google Quantum AI published a whitepaper demonstrating that the elliptic curve discrete logarithm problem over the secp256k1 and secp256r1 curves — the mathematical foundation underpinning Bitcoin’s ECDSA signature scheme and virtually every major blockchain — can be broken by a fault-tolerant quantum computer using fewer than 500,000 physical qubits, executable in minutes. This represents an approximately 20-fold reduction in estimated physical qubit requirements from prior best published estimates, and continues a decade-long exponential compression of the quantum resource cost for cryptographically relevant attacks.
This analysis, authored from the perspective of the QSHA256 research platform, situates Google’s findings within the post-quantum threat landscape tracked in real time. The QSHA256 Quantum Vulnerability Agent currently monitors 6,946,902 BTC LIVE across seven Bitcoin address types with quantum exposure. Google’s paper does not merely sharpen a theoretical threat — it materially accelerates the timeline within which that exposure becomes actionable for any adversary operating a sufficiently scaled cryptographically relevant quantum computer (CRQC). Every ECC-based chain — Bitcoin, Ethereum, Solana, and beyond — now has a deadline measured in engineering years, not theoretical decades.
Bitcoin’s cryptographic security rests on the elliptic curve discrete logarithm problem (ECDLP) over the secp256k1 curve, defined over a 256-bit prime field. Formally: given the generator point G and a public key Q = kG, recover the scalar k (the private key). The best classical algorithms for this problem — Pollard’s rho and baby-step giant-step — run in O(√n) ≈ 2128 group operations, placing brute-force attacks firmly in the infeasible regime for classical adversaries.
Shor’s algorithm, first described in 1994, dissolves this hardness assumption entirely on a fault-tolerant quantum computer. The algorithm encodes the elliptic curve group operation into a quantum circuit and exploits quantum parallelism via the Quantum Fourier Transform (QFT) to find the hidden period of a function related to the discrete logarithm. The recovery of k from Q becomes polynomial-time. The algorithm has been known for 30 years; what has been unknown is the hardware cost to execute it at cryptographic scale.
Google’s paper answers that question with unprecedented precision. They compiled two distinct quantum circuits implementing Shor’s algorithm for ECDLP-256:
| Circuit | Logical Qubits | Toffoli Gates | Physical Qubits (est.) | Runtime |
|---|---|---|---|---|
| A (qubit-optimized) | < 1,200 | ~90 million | < 500,000 | Minutes |
| B (gate-optimized) | < 1,450 | ~70 million | < 500,000 | Minutes |
The two circuits represent a space-time tradeoff: Circuit B uses slightly more logical qubits to reduce Toffoli gate count (and thus circuit depth). Both are executable under hardware capability assumptions consistent with Google’s Willow-class superconducting processors. The physical qubit estimate incorporates standard surface code error-correction overhead at error rates already demonstrated in laboratory hardware.
The critical metric here is Toffoli gate count, not raw circuit size. In fault-tolerant architectures, Toffoli gates (non-Clifford operations) require magic state distillation — an expensive subroutine that consumes the majority of qubit budget and runtime. The 70–90 million Toffoli range determines the actual execution time and magic state factory requirements. Google’s compilation achieves this count through novel arithmetic optimizations for elliptic curve point addition over secp256k1, reducing the modular multiplication circuit depth beyond what was previously published.
The chart below, reproduced from Google’s whitepaper, illustrates the historical compression in estimated physical qubit requirements to break ECDLP-256, alongside Toffoli gate count trends for quantum chemistry benchmark problems (FeMoco simulations). Both curves tell the same story: algorithmic progress is compressing the threat faster than hardware progress is expanding defensive timelines.
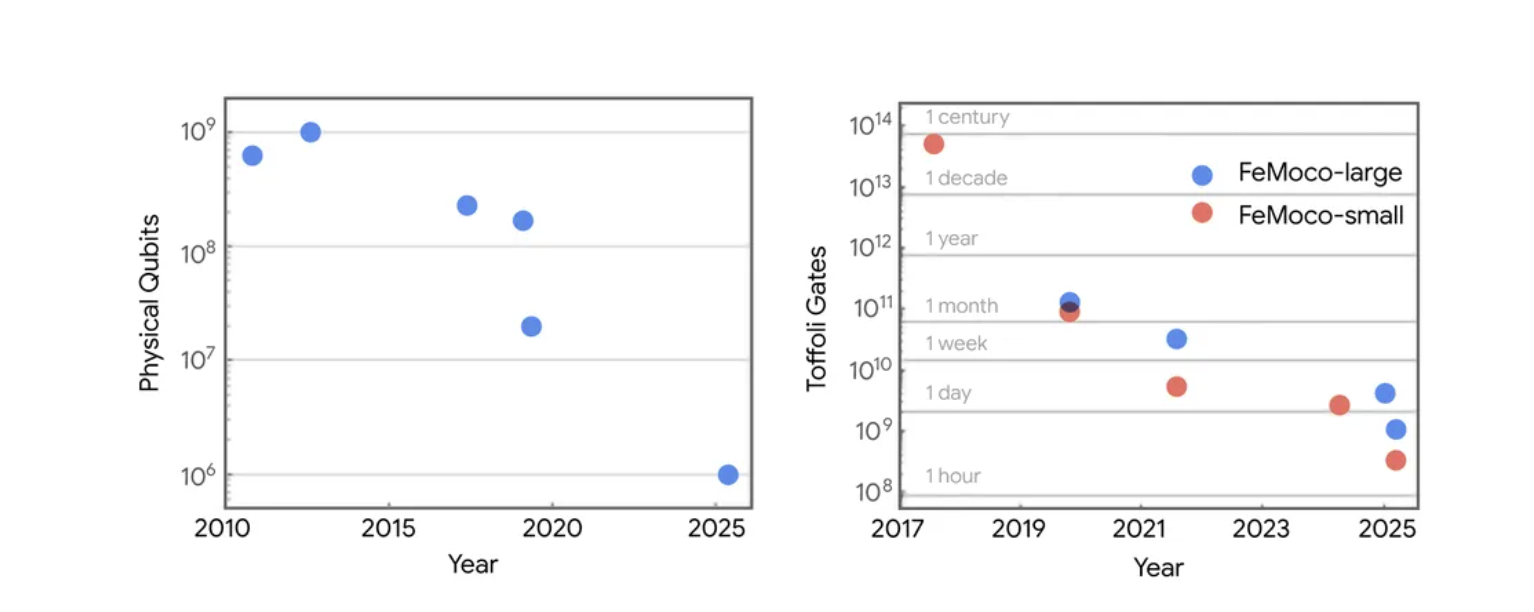
Figure 1 — Left: Physical qubit requirements to break ECDLP-256 over time, showing a ~1,000× reduction from 109 (2010) to under 106 (2025). Right: Toffoli gate counts for FeMoco-large and FeMoco-small quantum chemistry benchmarks (2017–2025). Source: Babbush & Neven, Google Quantum AI (2026).
The left panel of Figure 1 tells a stark story: from approximately 109 physical qubits in 2010–2012, the estimated requirement has compressed to under 106 by 2025 — three orders of magnitude in 15 years. This compression is driven entirely by algorithmic and compilation improvements, not hardware advances. The same physical error rates used in 2019 estimates apply here; what has changed is how efficiently those physical resources are used. This is a compounding algorithmic optimization story. There is no floor in sight.
The right panel shows identical compression dynamics in quantum chemistry (FeMoco), confirming this is not a cryptography-specific phenomenon. Every area of fault-tolerant quantum algorithm design is experiencing the same trajectory. The cryptographic community should find no comfort in the pace of quantum hardware development: the threat closes from the algorithmic side simultaneously and independently.
The QSHA256 Quantum Vulnerability Agent performs continuous block-by-block scanning of the Bitcoin blockchain, classifying UTXO exposure across seven script types. As of the latest scan, the platform tracks 6,946,902 BTC with some degree of quantum vulnerability — representing one of the largest concentration of cryptographically exposed digital assets on any public ledger.
The threat model differs critically by address type. It is essential to distinguish between structural exposure and conditional exposure:
Structurally exposed (public key always on-chain):
• P2PK (Pay-to-Public-Key): The uncompressed or compressed public key appears verbatim in the scriptPubKey. No spend event is required; the target for Shor’s algorithm is already publicly broadcast. These are legacy outputs from Bitcoin’s earliest blocks, including the Satoshi-era coinbase transactions. Every funded P2PK UTXO is immediately actionable by a CRQC.
• P2TR (Taproot): BIP-341 encodes a 32-byte x-only public key directly in the address. The full public key is trivially reconstructable (the x-coordinate uniquely determines both possible y-values; the correct one is resolved in a single step). All funded P2TR UTXOs expose the public key by construction, regardless of spend history.
• P2MS (Bare Multisig): All constituent public keys appear in the scriptPubKey. M-of-N multisig outputs broadcast every signatory’s public key at the time the UTXO is created.
Conditionally exposed (public key revealed upon spend):
• P2PKH, P2WPKH, P2SH, P2WSH: These outputs commit to a hash of the public key (or script hash), not the key itself. The public key is only revealed in the spending transaction’s scriptSig or witness. However: if an address has ever been used to spend funds, the public key is permanently on-chain. Any address that has been spent from and subsequently re-funded is at the same risk as a structurally exposed address. QSHA256 scans specifically for this pattern.
Google’s resource estimates do not change the exposure categories above — they change the urgency. At <500K physical qubits and a minutes-scale runtime, the attack crosses from “nation-state only” territory into the operational envelope of any organization capable of building and operating a next-generation quantum computer. Explore the interactive dual-attack mode (Shor’s algorithm vs. Grover’s algorithm) at ECDSA Signatures vs SHA-256 Hashing.
The most intellectually novel contribution of this paper is not the resource estimates themselves — it is the disclosure methodology.
Classical vulnerability disclosure has converged on Coordinated Vulnerability Disclosure (CVD), codified in ISO/IEC 29147:2018 and operationalized by CERT/CC and Google’s own Project Zero with its 90-day embargo model. CVD’s premise: give vendors time to patch before public disclosure. This works when systems are patchable — when a software vulnerability can be remediated faster than adversaries can exploit published details.
Blockchain systems are categorically different. A cryptocurrency network is a decentralized consensus mechanism whose security properties are inseparable from public confidence in those properties. Publishing detailed quantum resource estimates creates two distinct and partially opposed risks:
• Attack enablement: Specific circuit constructions and gate decompositions could be used directly by a well-resourced adversary to accelerate their own attack implementation. Publication of optimized Shor’s circuits for secp256k1 could cut years off an adversary’s development timeline.
• Confidence erosion via FUD: Vague, unsubstantiated, or inflated resource estimates create fear, uncertainty, and doubt without informing defense. Irresponsible quantum FUD is itself a class of attack on cryptocurrency market confidence and system stability, exploitable by short-sellers and adversarial actors who benefit from perceived fragility.
Google’s solution decouples verification from exploitation using a zero-knowledge proof (ZKP) of circuit correctness:
This is a significant methodological contribution to the quantum security disclosure field. It effectively decouples verification of a vulnerability claim from exploitation of that vulnerability — something that is impossible in most classical security contexts, where the vulnerability description IS the exploit. The ZKP functions as a cryptographic commitment: mathematically binding, publicly verifiable, and informationally inert with respect to attack construction.
Google additionally engaged with the U.S. government prior to publication and coordinated with Coinbase, the Stanford Institute for Blockchain Research, and the Ethereum Foundation on the cryptocurrency-specific implications. This is the first instance, to this author’s knowledge, of a responsible disclosure framework for quantum cryptanalytic vulnerabilities applied at institutional scale. We urge every quantum research team working on cryptanalytic resource estimation to adopt this model.
Google’s paper endorses post-quantum cryptography (PQC) as the well-understood migration path. The NIST PQC standardization process (finalized 2024) produced three primary standards with direct relevance to blockchain signature schemes:
| Standard | Algorithm Family | Sig Size | PK Size | Security Assumption |
|---|---|---|---|---|
| ML-DSA (CRYSTALS-Dilithium) | Lattice (Module LWE/SIS) | 2.4–4.6 KB | 1.3–2.6 KB | Module Lattice |
| SLH-DSA (SPHINCS+) | Hash-based (stateless) | 8–50 KB | 32–64 B | Collision-resistant hash |
| FALCON (NIST Round 4) | Lattice (NTRU) | 0.7–1.3 KB | 0.9–1.8 KB | NTRU lattice |
For Bitcoin specifically, the migration path runs through BIP-360 (P2QRH — Pay to Quantum Resistant Hash) and BIP-361, which define a new native SegWit output type and validation semantics for post-quantum signature schemes. See our detailed technical analysis: Bitcoin’s Post-Quantum Migration Path: BIP-360 & BIP-361.
The PQC migration is not merely a cryptographic substitution. It is a multi-year, multi-layer systems engineering challenge requiring:
• Soft-fork consensus activation across the global Bitcoin node network, requiring supermajority miner signaling and broad economic node adoption — a process that, historically, has taken 12–24+ months from proposal to activation even for non-controversial changes
• Wallet software upgrades across every UTXO holder — including custodians, exchanges, hardware wallets, and millions of self-custody users, many of whom hold seeds for addresses they have not accessed in years
• A migration window during which legacy quantum-vulnerable UTXOs remain spendable, creating a race condition: users must migrate before a CRQC becomes operational, but the network cannot force migration without consensus
• Abandoned UTXO policy: an estimated portion of the at-risk BTC belongs to permanently inaccessible addresses — lost keys, deceased holders, early mining output with no surviving access. These cannot be migrated by any mechanism. Google’s paper acknowledges this explicitly and notes it as a policy question for the cryptocurrency community.
Google’s specific short-term recommendation, actionable immediately at zero cost: refrain from address reuse and avoid exposing public keys unnecessarily. Every Bitcoin holder with funds in an address whose public key has been revealed on-chain through any prior spend should migrate those funds to a fresh address with an unexposed key. This does not require a protocol change. It requires only wallet hygiene.
Google has publicly committed to completing its own internal cryptographic migration to PQC by 2029. This date, paired with today’s paper, should be read as a coordinated public statement of the threat timeline: Google believes that by 2029, the window for safe migration may be closing. The paper names three external institutional partners on the cryptocurrency implications:
• Coinbase — the largest US-regulated cryptocurrency exchange, holding custodial responsibility for a significant fraction of on-chain BTC across millions of users
• Stanford Institute for Blockchain Research — the primary academic research coordination body for blockchain cryptography in North America
• Ethereum Foundation — the governance body for the Ethereum network, which uses the same secp256k1 curve as Bitcoin and faces an identical ECDLP-256 exposure across its entire UTXO (account state) set
The coordination of these institutions signals that today’s paper is not an academic exercise. It is the opening move of an industry-wide migration campaign backed by the world’s leading quantum computing organization. Google’s 2029 target should be read as a forcing function, not a distant horizon. Organizations that have not completed PQC migration by 2029 will be operating with cryptographic infrastructure that Google considers imminently breakable.
For Bitcoin specifically, the 2029 window is extraordinarily tight. BIP-360 and BIP-361 remain in draft. The Bitcoin developer community has not yet reached consensus on a PQC signature scheme, on the block size implications of larger PQC signatures, or on the governance of abandoned UTXO migration. The combination of Google’s compressed resource estimates and a 3-year migration window creates a genuine systemic risk scenario. QSHA256’s Quantum Vulnerability Agent provides the most granular publicly available quantification of that risk: per-block, per-address-type, with live BTC exposure tracking.
Bitcoin is not alone. The secp256k1 and secp256r1 curves underpin the signature schemes of virtually every major public blockchain:
• Ethereum — uses secp256k1 for EOA (externally owned account) signatures; ~100 million active addresses with exposed or exposable public keys
• Solana — uses Ed25519 (a different curve, Curve25519), which faces a similar ECDLP vulnerability under Shor’s algorithm; the mathematical structure differs but the attack principle is identical
• Litecoin, Bitcoin Cash, Dogecoin, and all Bitcoin forks — inherit secp256k1 directly; all face identical exposure
• EVM-compatible chains (Polygon, Avalanche, BNB Chain, etc.) — use Ethereum-compatible cryptography; Google’s estimates apply directly
Every ECC chain now has the same deadline: the point at which a sufficiently scaled fault-tolerant quantum computer becomes operational. Google has demonstrated, with mathematical proof, that this deadline is achievable at under 500,000 physical qubits. IBM’s quantum roadmap targets 100,000+ physical qubits by 2026–2027. The path from 100K to 500K is an engineering question, not a scientific one.
The question every ECC chain must now answer is not “are we quantum-vulnerable?” — that has been settled. The question is “what is our migration plan, and will it complete before the hardware catches up?”
Google’s March 31, 2026 whitepaper is a watershed event. It compresses the estimated physical qubit threshold for breaking ECDLP-256 by approximately 20× to under 500,000 — within the engineering trajectory of quantum hardware programs already underway. It introduces a novel responsible disclosure methodology using zero-knowledge proofs that should become the field standard for quantum cryptanalytic research. It explicitly calls on the cryptocurrency ecosystem to accelerate the transition to post-quantum cryptography. And it backs that call with coordinated institutional support from Google, Coinbase, Stanford, and the Ethereum Foundation.
What remains unknown is the precise hardware roadmap: when will a fault-tolerant superconducting quantum computer reach 500,000 physical qubits with the coherence times and gate fidelities required for a sustained multi-minute computation? The historical compression curve in Figure 1 suggests the algorithmic target will continue moving downward even as hardware scales up. The intersection of those two curves is Q-Day.
What QSHA256 provides is a live accounting of exactly how much is at stake: 6,946,902 BTC in quantum-vulnerable UTXOs, tracked block by block, address type by address type, updated continuously by the Quantum Vulnerability Agent. Google has now told the world — with mathematical proof — that the machine capable of taking it is closer than anyone previously calculated.
Every ECC chain now has a deadline. The clock is already running.
Explore the live exposure data at Quantum Vulnerability Agent. Analyze the ECDSA vs SHA-256 threat split at Bitcoin Risk Visualizer. Read the BIP-360 migration analysis at Bitcoin’s Post-Quantum Migration Path. Compare PQC signature sizes at Size Matters.
• [1] Babbush, R. & Neven, H. (2026). Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly. Google Quantum AI. Whitepaper PDF
• [2] Google. (2026). Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly. Google Research Blog. research.google/blog
• [3] Google. (2026). Our 2029 timeline for completing our cryptography migration. Google Blog. blog.google
• [4] Google. (2026). The quantum era is coming — are we ready to secure it? Google Blog. blog.google
• [5] QSHA256 Quantum Vulnerability Agent. (2026). Live Bitcoin quantum exposure data. qsha256.com/quantum-agent
• [6] Shor, P. W. (1994). Algorithms for quantum computation: discrete logarithms and factoring. FOCS 1994.
• [7] NIST. (2024). Post-Quantum Cryptography Standards: ML-DSA (FIPS 204), SLH-DSA (FIPS 205), ML-KEM (FIPS 203).