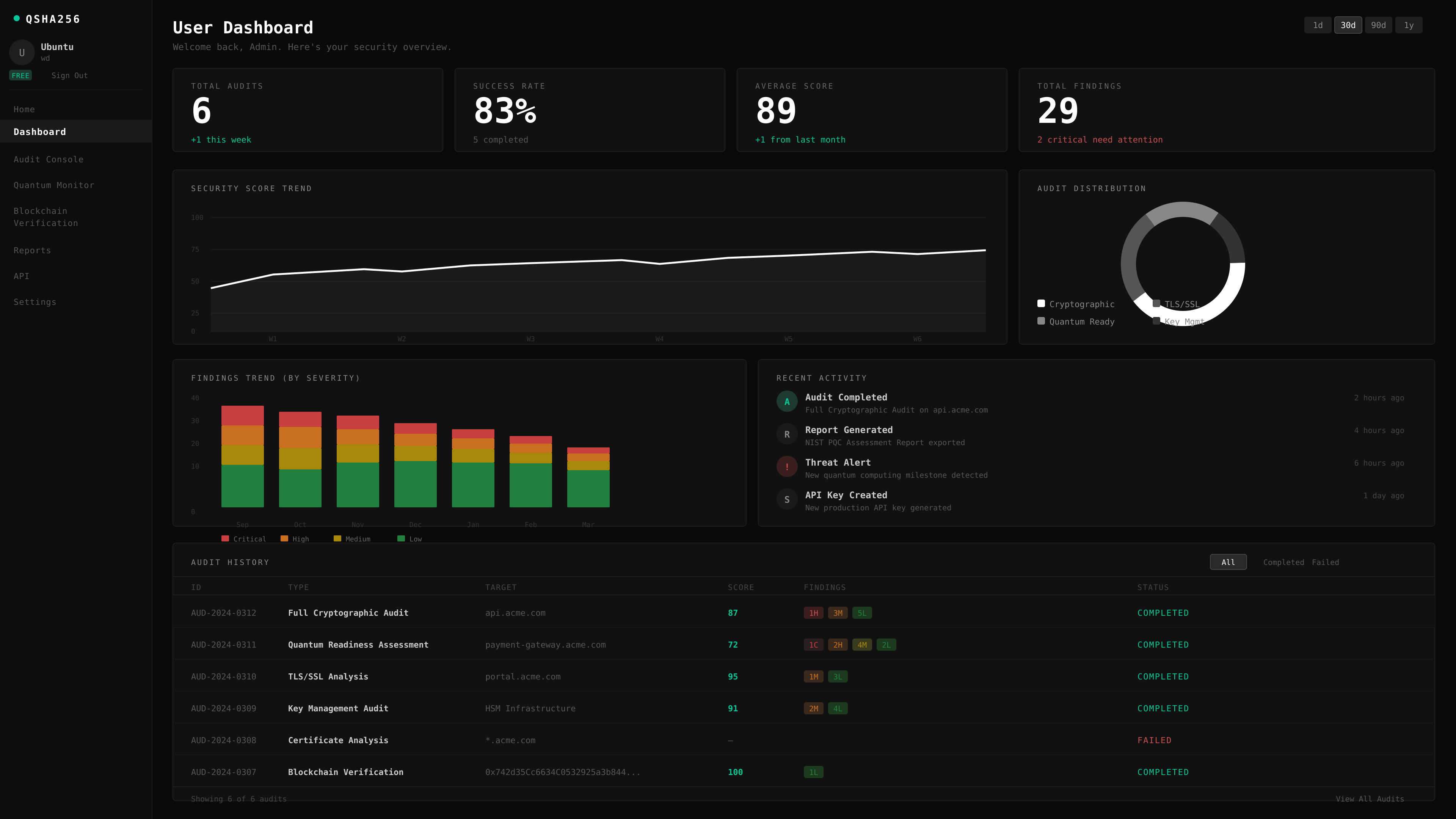
Our Solutions
QSHA256 provides post-quantum security auditing, cryptographic validation, and live monitoring dashboards to protect critical systems from both classical cyber threats and future cryptographically relevant quantum computers (CRQC). The platform secures Blockchain & Web3 infrastructure, FinTech systems, AI & machine learning environments, biomedicine research platforms, chemistry and simulation systems, and cybersecurity infrastructure, using real-world quantum testing and methodologies aligned with NIST post-quantum standards and global regulatory frameworks to ensure long-term resilience and compliance.
More Information →