Two Breakthroughs, One Broken Curve: QLDPC Architecture and Optimized Shor’s Circuits Converge on secp256k1
Within a six-week window in early 2026, two independent research teams published results that individually would have reshaped the post-quantum security landscape — and together constitute the strongest evidence to date that cryptographically relevant quantum computers are an engineering problem, not a theoretical aspiration. The Pinnacle Architecture (Webster et al., Iceberg Quantum, February 12, 2026) demonstrated that RSA-2048 can be factored using fewer than 100,000 physical qubits via quantum low-density parity check (QLDPC) error correction codes. Six weeks later, Google Quantum AI (Babbush & Neven, March 31, 2026) published compiled Shor’s algorithm circuits for the elliptic curve discrete logarithm problem over secp256k1 — Bitcoin’s actual curve — executable with fewer than 500,000 physical qubits in approximately 9 minutes.
These teams did not coordinate. They used different error correction paradigms. They attacked different cryptographic problems. They arrived at the same conclusion: the hardware threshold for breaking public-key cryptography has dropped below 500,000 physical qubits, and is likely to drop further. This is the QSHA256 synthesis of what both results mean — separately, together, and for the 6,946,902 BTC LIVE currently tracked at quantum risk on this platform.
Processing units: Modular QLDPC code blocks that perform arbitrary logical Pauli product measurements per cycle — the primitive operation of fault-tolerant computation — without decode/re-encode overhead.
Magic engines: Dedicated QLDPC blocks for magic state distillation and injection, eliminating the largest qubit budget bottleneck in surface code architectures.
Connectivity: Quasi-local only — practical for real hardware. Modular design allows space-time tradeoff (more units = faster runtime).
Result: RSA-2048 at ~100,000 physical qubits, ~1 month runtime (single processing unit).
Circuit compilation: Two compiled Shor’s algorithm circuits for ECDLP over secp256k1, with novel arithmetic optimizations for elliptic curve point addition reducing Toffoli gate count beyond prior published work.
Disclosure method: Zero-knowledge proof of circuit correctness — verifies resource estimates without revealing the attack construction, preventing the paper from serving as an attack roadmap.
Coordination: Pre-publication engagement with U.S. government; coordination with Coinbase, Stanford, and Ethereum Foundation.
Result: secp256k1 private key recovery in ~9 minutes at <500,000 physical qubits.
| Dimension | Pinnacle Architecture | Google ECDLP Disclosure |
|---|---|---|
| Published | Feb 12, 2026 | March 31, 2026 |
| Authors / Institution | Webster et al., Iceberg Quantum (Sydney) | Babbush & Neven, Google Quantum AI |
| Cryptographic Target | RSA-2048 (integer factorization) | ECDLP-256 / secp256k1 (elliptic curve DLP) |
| Quantum Algorithm | Shor’s (modular exponentiation) | Shor’s (elliptic curve group arithmetic) |
| Error Correction | QLDPC codes (breakthrough) | Surface codes (optimized) |
| Physical Qubits | ~100,000 | <500,000 |
| Logical Qubits | ~2,048 (modular arithmetic) | 1,200–1,450 (two circuits) |
| Key Gate Metric | T-gates / magic states | Toffoli gates (70–90 million) |
| Runtime | ~1 month (single processing unit) | ~9 minutes |
| Bitcoin Relevance | Indirect — RSA harder than ECDSA | Direct — secp256k1 IS the target |
| Disclosure Method | Standard academic paper | Zero-knowledge proof (novel) |
| Hardware Assumption | 10³ physical error rate, 1µs cycle | Willow-class superconducting qubits |
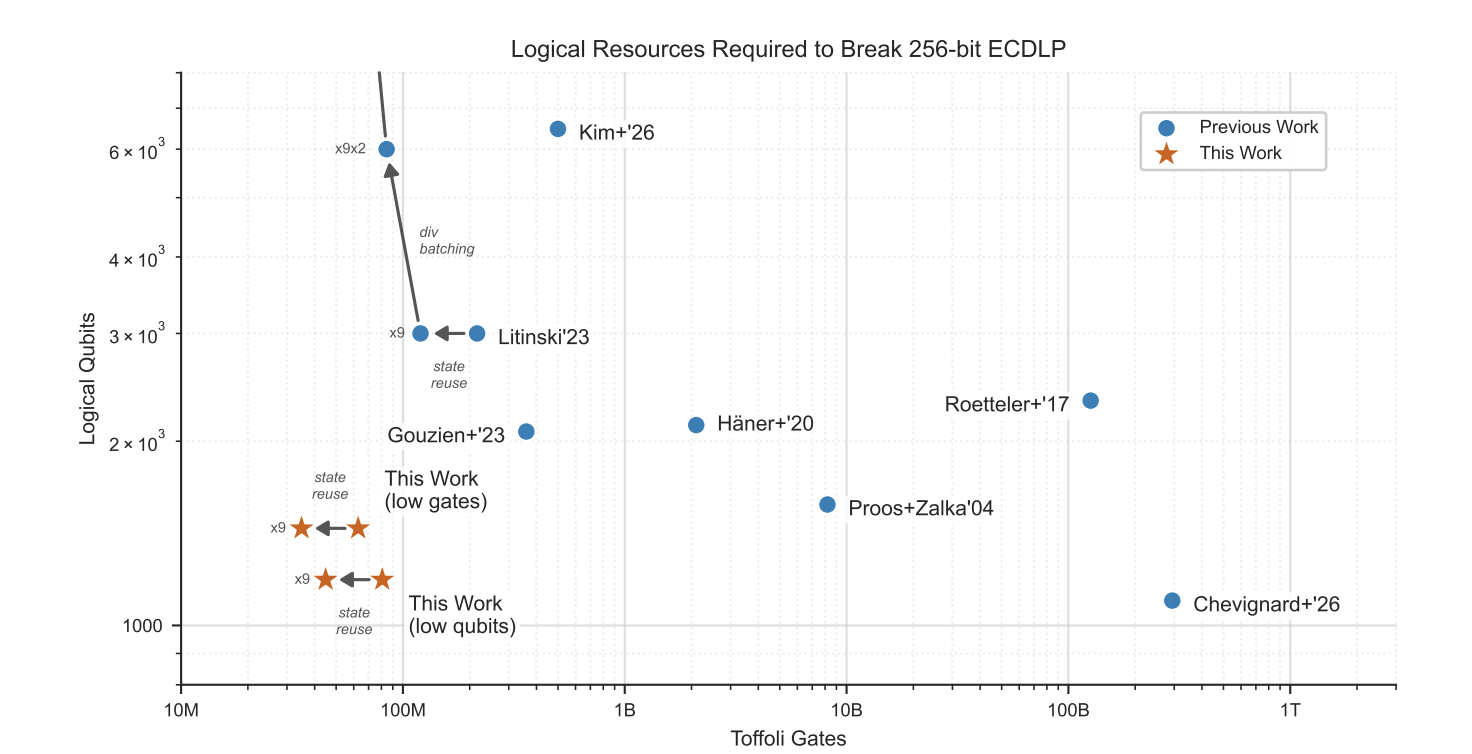
Figure 1 — Logical qubits vs Toffoli gates for breaking 256-bit ECDLP. Blue dots: prior work (Roetteler’17, Häner’20, Proos+Zalka’04, Litinski’23, Kim+’26). Orange stars: Google’s compiled circuits (“This Work”). Source: Babbush & Neven, Google Quantum AI (2026).
This chart defines the current Pareto frontier for breaking secp256k1. Prior published work required between 1,000 and 6,000 logical qubits and between 100 million and 1 trillion Toffoli gates. Google’s two compiled circuits (“This Work”, orange stars) achieve 1,200–1,450 logical qubits at 70–90 million Toffoli gates — a new frontier that dominates all prior work on both axes simultaneously.
The Toffoli gate count is the operationally critical metric. In fault-tolerant architectures using surface codes, Toffoli gates (non-Clifford operations) require magic state distillation — an expensive subroutine that consumes the majority of physical qubit budget and runtime. Reducing Toffoli count from the prior best (~100M, Litinski’23) to 70M (Google’s gate-optimized circuit) is what drives the ~9-minute runtime. Logical qubits here are error-corrected qubits; each requires hundreds of physical qubits under surface code overhead, yielding the <500K physical qubit estimate when the encoding ratio is applied.
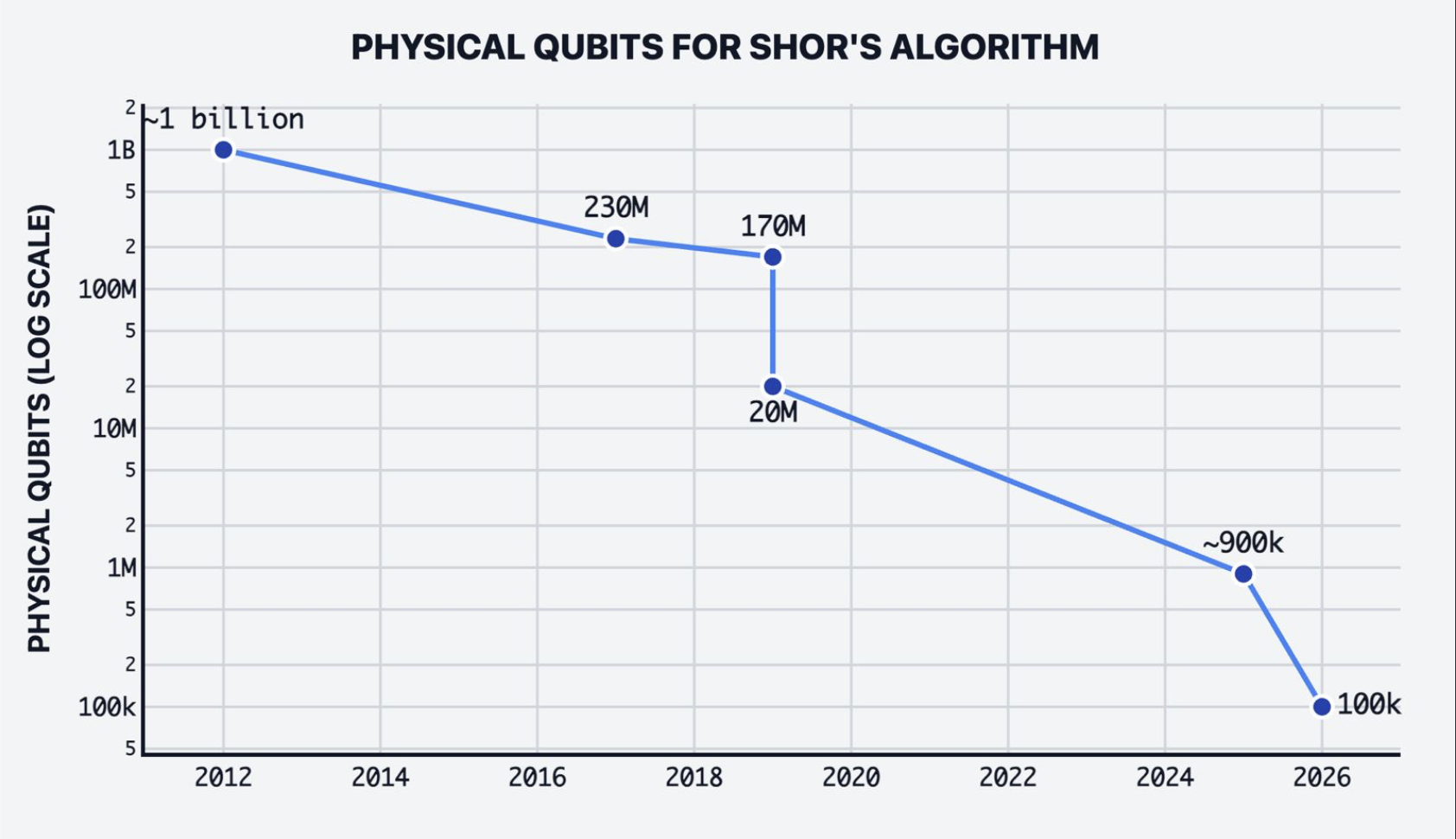
RSA-2048: ~1B qubits (2012) → ~100K (2026). Source: Pinnacle Architecture, Iceberg Quantum.
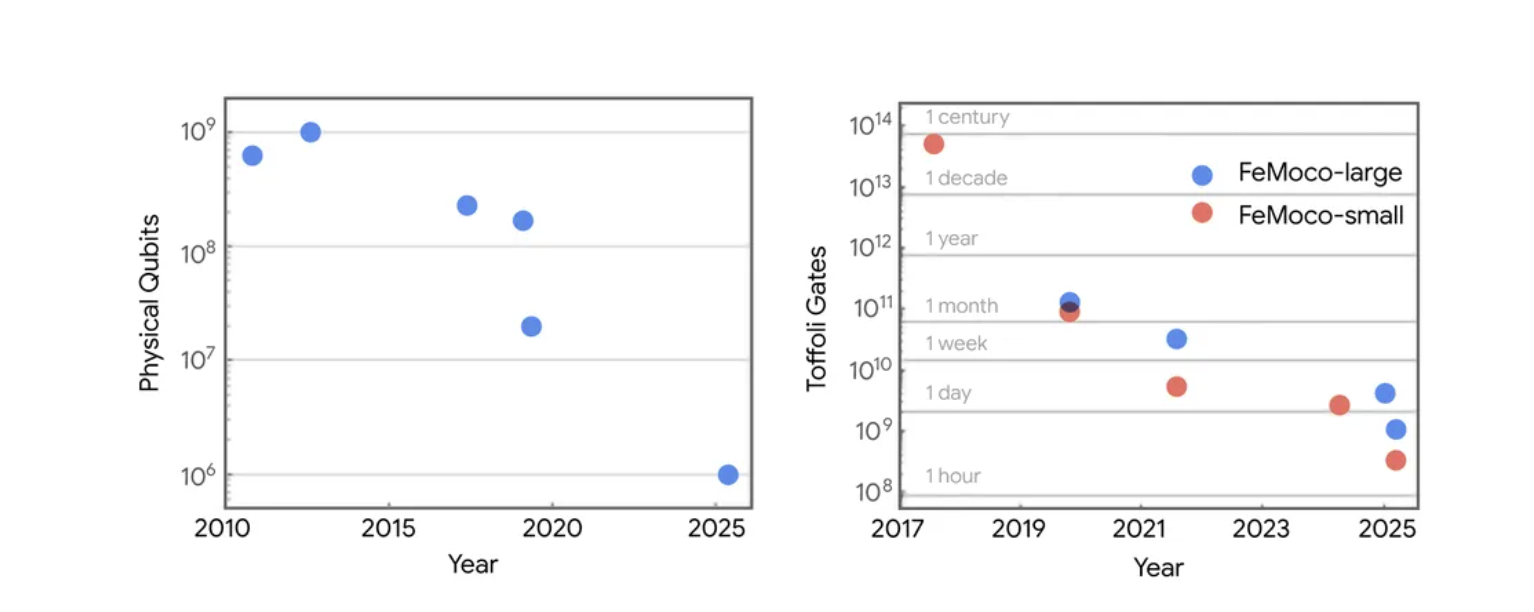
ECDLP-256: ~109 qubits (2010) → <106 (2025). Source: Google Quantum AI (2026).
Both curves display the same exponential compression over 15 years — three orders of magnitude for RSA, three orders of magnitude for ECC. Critically, this compression is driven entirely by algorithmic and compilation improvements, not hardware advances. The physical error rates used in 2019 estimates are the same ones used today. What has changed is how efficiently those physical resources are deployed. Both curves show no floor in sight.
Note the asymmetry: RSA-2048 falls at 100K physical qubits under QLDPC. ECDLP-256 falls at <500K physical qubits under surface codes. RSA-2048 is computationally harder than ECDSA-256 — it requires more logical qubits and more gate depth under Shor’s algorithm. The fact that it falls at fewer physical qubits is the Pinnacle Architecture’s QLDPC advantage: the more efficient error correction more than compensates for the larger problem size.
This synthesis is the most important finding neither paper makes explicitly. The Pinnacle Architecture paper does not apply QLDPC to ECC. The Google paper does not apply QLDPC to their compiled circuits. Both results are valid within their own error correction framework. But the field is not static — and the history of both curves above demonstrates that algorithmic improvements compound. The next major compression event will likely be QLDPC-compiled ECC circuits. When that paper appears, the physical qubit threshold for breaking secp256k1 may be revised downward by the same 9× factor Pinnacle applied to RSA.
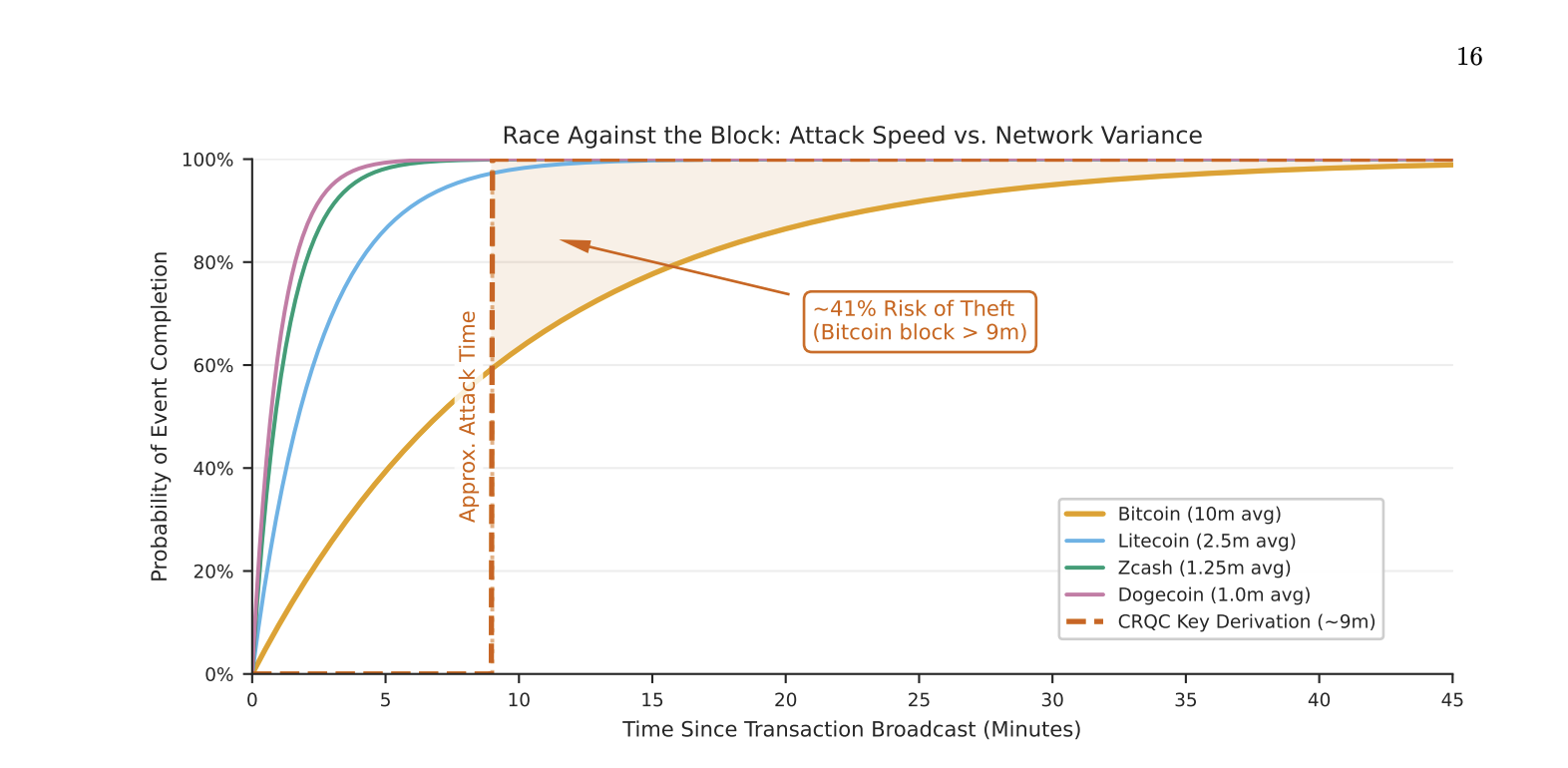
Figure 2 — Probability of event completion vs. time since transaction broadcast. CRQC approximate attack time: ~9 minutes (dashed). Bitcoin (10m avg): ~41% risk of theft. Litecoin (2.5m), Zcash (1.25m), Dogecoin (1.0m) largely safe. Source: Google Quantum AI (2026).
This is the most operationally alarming chart in either paper. Google’s compiled Shor’s circuit derives a secp256k1 private key in approximately 9 minutes. Bitcoin’s average block confirmation time is 10 minutes. The shaded region between the two curves is the attack window — the gap during which a CRQC operator has completed the key derivation but the legitimate transaction has not yet been confirmed in a block.
The chart quantifies this precisely: ~41% probability of theft for a Bitcoin transaction broadcast to the mempool when a CRQC is operating. That 41% represents the probability that, when a user broadcasts a transaction exposing their public key (which happens in the spending input of every P2PKH, P2WPKH, and similar transaction), the CRQC completes the attack before a miner confirms the block.
This is not a static balance attack or a theoretical future scenario — it is a race condition that exists in the protocol today, gated only on the hardware. The chains with faster block times fare better: Litecoin (2.5m avg), Zcash (1.25m), and Dogecoin (1.0m) all achieve near-100% confirmation before a 9-minute CRQC attack completes. Bitcoin’s 10-minute target block time, chosen in 2008 for entirely different reasons, inadvertently creates maximum exposure to this attack.
Structurally exposed addresses — P2PK, P2TR, P2MS — do not require an active transaction. Their public keys are permanently on-chain. The Race Against the Block applies specifically to the transactional tier: addresses being actively spent from in real time.
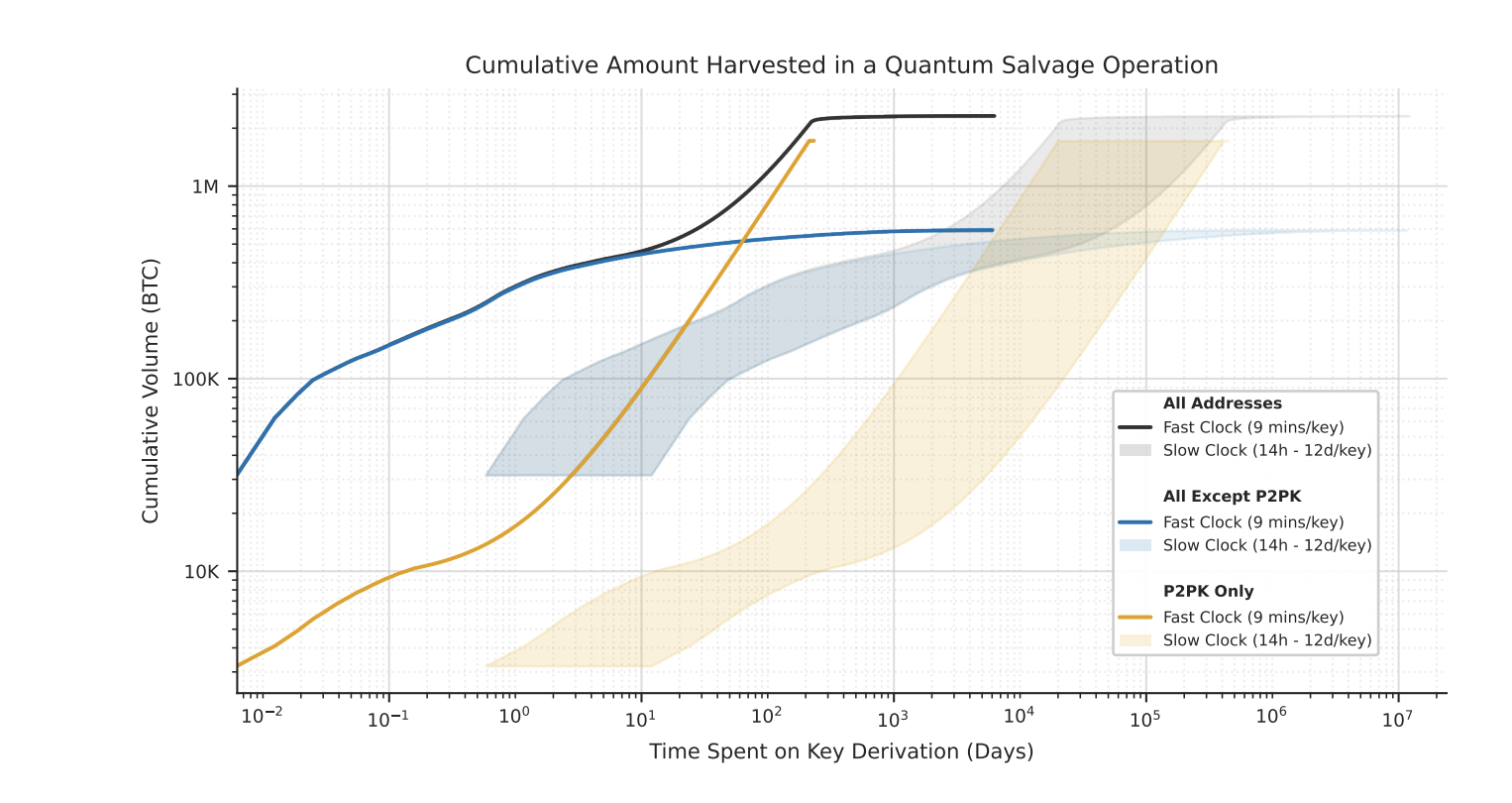
Figure 3 — Cumulative BTC harvested in a sustained quantum salvage operation. Fast Clock (9 min/key): black = all addresses, blue = all except P2PK, orange = P2PK only. Shaded bands = slow clock (14h–12 days/key). Source: Google Quantum AI (2026).
This chart models what a coordinated, sustained CRQC operation targeting Bitcoin’s at-risk UTXOs looks like over time. Two speed regimes are modeled:
• Fast Clock (9 min/key): Consistent with Google’s compiled circuit runtime. P2PK-only addresses (orange) reach approximately 1 million BTC within ~200 days. All addresses combined (black) plateau at ~1–2 million BTC as the accessible P2PK supply is exhausted and the operation shifts to harder targets.
• Slow Clock (14h–12 days/key): Consistent with less optimized hardware or deliberate targeting of high-value wallets. The same trajectory plays out over years instead of days, with wide uncertainty bands reflecting variance in individual address balances and CRQC performance.
QSHA256 currently tracks 6,946,902 BTC at quantum risk across 7 address types, monitored block-by-block at Quantum Vulnerability Agent. This figure is the cumulative harvest curve for that exposure pool. The three exposure tiers:
• Structural exposure (immediate): P2PK, P2TR, P2MS — public key always on-chain. No transaction required to initiate attack. These are the Fast Clock’s first targets.
• Transactional exposure (Race Against the Block): P2PKH, P2WPKH, P2SH, P2WSH with prior spends — public key revealed in spending transaction input. Attack must complete before block confirmation.
• Latent exposure (safe until spent): Addresses with no prior spend history — public key not yet on-chain. Safe as long as the holder does not broadcast a spending transaction during a period of CRQC operation.
In scientific research, independent corroboration is the gold standard of evidence. When two uncoordinated teams arrive at the same conclusion using different methods, that agreement is not coincidence — it is convergence. The Pinnacle Architecture and Google’s ECDLP disclosure are not merely two data points; they are two independent confirmations of the same underlying reality: the resource cost of breaking public-key cryptography has dropped below 500,000 physical qubits and is still falling.
Both papers also confirm that the primary driver of this compression is algorithmic progress, not hardware progress. Physical error rates and qubit connectivity requirements have not changed significantly since 2019. What has changed is how efficiently the same physical resources are marshaled. This is significant because algorithmic improvements are not constrained by the same engineering timelines as hardware. A new compilation technique — like QLDPC applied to ECC arithmetic — can appear as a preprint overnight and immediately revise the threat model.
The six-week window between these two papers is not a coincidence of timing — it reflects a broader acceleration in fault-tolerant quantum computing research that both teams are responding to independently. The field is moving. The threshold is falling. The two curves above have not stopped compressing.
See the individual analyses: The Pinnacle Architecture: RSA-2048 Breakable with 100K Qubits · Google Just Moved Q-Day — Every ECC Chain Now Has a Deadline
The Pinnacle Architecture proved that QLDPC error correction can collapse the physical qubit requirement for attacking RSA-2048 to 100,000 — below what any current quantum hardware vendor has shipped, but squarely within roadmap targets for 2026–2028. Google proved that secp256k1 private key recovery can be compiled to a circuit executable in ~9 minutes at under 500,000 physical qubits using today’s best surface code techniques.
Neither result alone would change the consensus view on Q-Day timing. Together, as independent corroboration from separate institutions using separate methods, they constitute the most significant update to the post-quantum threat timeline since Shor’s original 1994 paper. The remaining question is not whether the hardware will arrive — it is when, and whether the PQC migration of Bitcoin and every ECC chain will be complete before it does.
QSHA256 provides the most granular real-time answer to what is at stake: 6,946,902 BTC tracked across 7 address types, updated block-by-block. The quantum salvage operation modeled in Figure 3 begins the moment a CRQC crosses the 500K qubit threshold. Two papers published six weeks apart have now bracketed that threshold from both sides.
Live exposure data: Quantum Vulnerability Agent · Attack mode comparison: ECDSA vs SHA-256 · PQC signature sizes: Size Matters · Migration path: BIP-360 & BIP-361
• [1] Webster, P. et al. (2026). The Pinnacle Architecture: Reducing the cost of breaking RSA-2048 to 100,000 physical qubits using quantum LDPC codes. Iceberg Quantum. arXiv:2602.11457
• [2] Babbush, R. & Neven, H. (2026). Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly. Google Quantum AI. Whitepaper PDF
• [3] Google. (2026). Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly. Google Research Blog. research.google/blog
• [4] Shor, P. W. (1994). Algorithms for quantum computation: discrete logarithms and factoring. FOCS 1994.
• [5] NIST. (2024). Post-Quantum Cryptography Standards: ML-DSA (FIPS 204), SLH-DSA (FIPS 205), ML-KEM (FIPS 203).
• [6] QSHA256 Quantum Vulnerability Agent. qsha256.com/quantum-agent